- Home
- Mobiles
- Mobiles News
- Google's Project Vault Puts a Secure, Encrypted Computer Inside a microSD Card
Google's Project Vault Puts a Secure, Encrypted Computer Inside a microSD Card
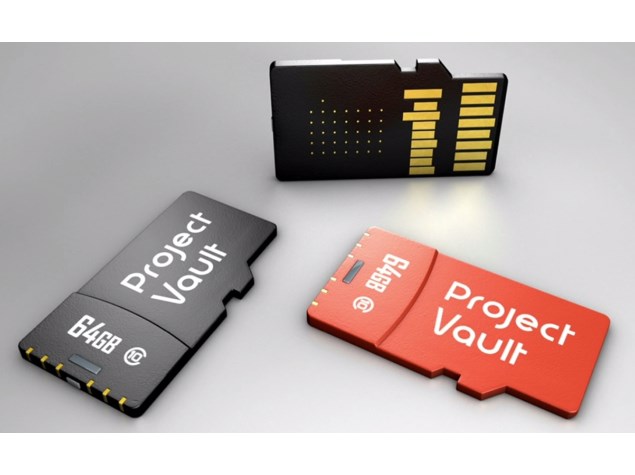
The fingernail-sized device runs on a custom ARM processor and has 4GB of secure storage space. It runs its own security-centric real-time OS with built in cryptographic infrastructure including a suite of encryption services and a hardware random-number generator. It has its own NFC hardware including an antenna, which can be used to authenticate users based on a physical token in their possession. The microSD interface suffices for all data input and output.
Google claims the Vault is completely transparent to its host devices and shows up as any ordinary storage destination. It is completely device- and OS-agnostic and only needs to be plugged in to work. Compatible apps can interact with two dedicated files: one that must be written to and the other that can only be read from. The rest of its file system is fake, and any interaction with it will result in a standard "bad sector" error, preventing even the host device from seeing what goes in and out of the Vault. No special drivers or user intervention are required. This means that a user's security is maintained even if he or she moves the Vault between multiple host devices, no matter how insecure they might be.
The device and its software support text messaging, voice, and video streaming, as long as parties on both ends have their own Vault cards. Immutable hardware logging features would help owners determine if anyone has tried tampering with their Vault. Google is using 500 prototype cards internally and hopes to have commercial products out soon, with enterprise customers targeted first and consumer applications rolling out later. An open-source kit including development hardware and source code is already available.
For the latest tech news and reviews, follow Gadgets 360 on X, Facebook, WhatsApp, Threads and Google News. For the latest videos on gadgets and tech, subscribe to our YouTube channel. If you want to know everything about top influencers, follow our in-house Who'sThat360 on Instagram and YouTube.
Related Stories
- Galaxy S24 Series
- MWC 2024
- Apple Vision Pro
- Oneplus 12
- iPhone 14
- Apple iPhone 15
- OnePlus Nord CE 3 Lite 5G
- iPhone 13
- Xiaomi 14 Pro
- Oppo Find N3
- Tecno Spark Go (2023)
- Realme V30
- Best Phones Under 25000
- Samsung Galaxy S24 Series
- Cryptocurrency
- iQoo 12
- Samsung Galaxy S24 Ultra
- Giottus
- Samsung Galaxy Z Flip 5
- Apple 'Scary Fast'
- Housefull 5
- GoPro Hero 12 Black Review
- Invincible Season 2
- JioGlass
- HD Ready TV
- Laptop Under 50000
- Smartwatch Under 10000
- Latest Mobile Phones
- Compare Phones
- Huawei Pura 70 Pro+
- Huawei Pura 70 Ultra
- Tecno Camon 30 Premier 5G
- Motorola Edge 50 Fusion
- Oppo A1i
- Oppo A1s
- Motorola Edge 50 Ultra
- Leica Leitz Phone 3
- Asus ZenBook Duo 2024 (UX8406)
- Dell Inspiron 14 Plus
- Realme Pad 2 Wi-Fi
- Redmi Pad Pro
- Cult Shock X
- Fire-Boltt Oracle
- Samsung Samsung Neo QLED 8K Smart TV QN800D
- Samsung Neo QLED 4K Smart TV (QN90D)
- Sony PlayStation 5 Slim Digital Edition
- Sony PlayStation 5 Slim
- IFB 2 Ton 3 Star Inverter Split AC (CI2432C323G1)
- Daikin 1 Ton 3 Star Inverter Split AC (FTKL35UV16W+RKL35UV16W)














