- Home
- Laptops
- Laptops News
- Researchers Show Hacking Your Computer's BIOS is Child's Play
Researchers Show Hacking Your Computer's BIOS is Child's Play
Two security researchers have demonstrated an easy way to attack the BIOS chips on millions of PCs in under two minutes, undermining all physical and software security and potentially allowing encrypted data including passwords to be stolen. The two suggest that this technique has most likely already been used by the US National Security Agency.
In a talk titled How Many Million BIOSes Would You Like to Infect at this year's CanSecWest conference, researchers Corey Kallenberg and Xeno Kovah showed how vulnerable the UEFI BIOS implementations on all modern motherboards are. The problem, they said, is made even worse because users rarely patch their BIOS chips when updates are released by manufacturers.
The UEFI BIOS on modern PCs is a miniature operating system itself, and is invisible to desktop antimalware programs. By taking control of it, attackers can either disable a PC entirely or subvert its functions. What's more dangerous is that direct access to data in memory is possible, which means attackers can extract encryption keys, passwords, and other data even when so-called secure operating systems are used.
Even those using the Tails OS on a secure read-only medium, as popularised by Edward Snowden in his handling of leaked government files, would be vulnerable since the attack happens at a lower level than the OS. The victim would never even know he or she had been compromised.
The duo, who founded the firmware-focused security company LegbaCore, showed off a proof-of-concept attack called LightEater, which affects all motherboard vendors and system integrators thanks to the high degree of similarity in code between UEFI BIOS implementations. The attack breaks into a System Management Mode (SMM) which provides deeper access than even administrator and root modes.
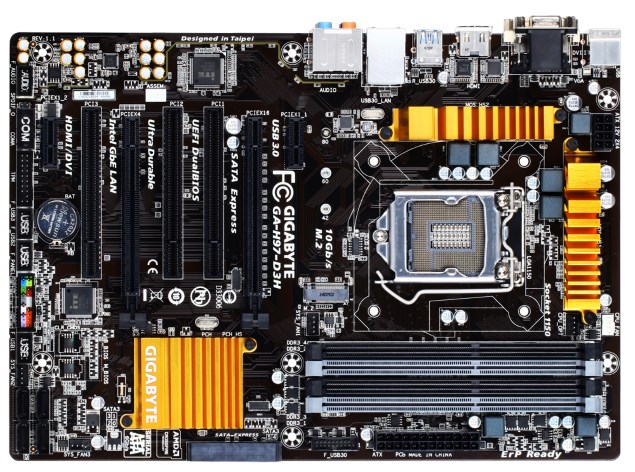
LightEater was able to compromise a variety of PCs from different vendors, all in under two minutes. Some Gigabyte motherboards were found to have particularly bad flaws in their access control security, but in all cases the primary fault was that BIOSes are nearly always unpatched.
Kallenberg and Kovah are marketing diagnostic tools to manufacturers in order to help them scan for such vulnerabilities and hopefully then create patches. However they are reasonably certain that the NSA and other similarly equipped agencies have been exploiting this vulnerability for a long time.
For the latest tech news and reviews, follow Gadgets 360 on X, Facebook, WhatsApp, Threads and Google News. For the latest videos on gadgets and tech, subscribe to our YouTube channel. If you want to know everything about top influencers, follow our in-house Who'sThat360 on Instagram and YouTube.
Related Stories
- AI
- iPhone 16 Leaks
- Apple Vision Pro
- Oneplus 12
- iPhone 14
- Apple iPhone 15
- OnePlus Nord CE 3 Lite 5G
- iPhone 13
- Xiaomi 14 Pro
- Oppo Find N3
- Tecno Spark Go (2023)
- Realme V30
- Best Phones Under 25000
- Samsung Galaxy S24 Series
- Cryptocurrency
- iQoo 12
- Samsung Galaxy S24 Ultra
- Giottus
- Samsung Galaxy Z Flip 5
- Apple 'Scary Fast'
- Housefull 5
- GoPro Hero 12 Black Review
- Invincible Season 2
- JioGlass
- HD Ready TV
- Laptop Under 50000
- Smartwatch Under 10000
- Latest Mobile Phones
- Compare Phones
- iQOO Z9x
- iQOO Z9
- HMD Pulse
- HMD Pulse+
- HMD Pulse Pro
- Realme Narzo 70x 5G
- Realme Narzo 70 5G
- Samsung Galaxy C55
- Lenovo IdeaPad Pro 5i
- Asus ZenBook Duo 2024 (UX8406)
- Realme Pad 2 Wi-Fi
- Redmi Pad Pro
- boAt Storm Call 3
- Lava ProWatch Zn
- Samsung Samsung Neo QLED 8K Smart TV QN800D
- Samsung Neo QLED 4K Smart TV (QN90D)
- Sony PlayStation 5 Slim Digital Edition
- Sony PlayStation 5 Slim
- Lloyd 1.5 Ton 3 Star Inverter Split AC (GLS18I3FOSEW)
- Haier 1.5 Ton 3 Star Triple Inverter Split AC (HSU18K-PYSS3BN-INV)

















