- Home
- Internet
- Internet News
- Chrome exposes user passwords in plain text without additional verification
Chrome exposes user passwords in plain-text without additional verification
By Anupam Saxena | Updated: 9 August 2013 09:32 IST
Advertisement
If you've enabled Google Chrome's 'Offer to save passwords I enter on the web' feature and have saved some or all of your passwords through it, you should remember to sign-out of your Google account in Chrome, especially if you use the browser on a shared computer.
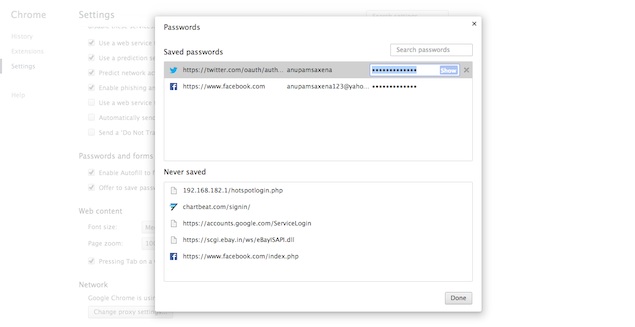
Google's popular Web browser allows you to save your passwords and manage them through a menu in the browser's Settings page. When you click on 'Manage saved passwords' you get a list of your Saved passwords as well as a list of websites where you have instructed the browser to 'never save'. Interestingly, when you click on one of your saved passwords, Google gives you the option to see the password in plain text by clicking on the 'Show' button which is placed along with the listing. It doesn't ask for a confirmation or any additional verification by, say, prompting for your Google account's password.
 It's worth pointing out that this 'vulnerability' - or feature as Google calls it (see below) - has been present in Chrome since its early days.
It's worth pointing out that this 'vulnerability' - or feature as Google calls it (see below) - has been present in Chrome since its early days.
Once signed in to your Google account on Chrome, the browser pulls all your bookmarks, browsing history and passwords. This means that if you forget to sign out while using Chrome on a shared computer, anyone will be able to access your saved passwords easily. Or someone sitting next to you while you are using the computer can distracting you momentarily. Someone accessing your computer remotely can also see these passwords, if you're not constantly supervising. The intruder can change the password and block access to your service accounts, as well.
Software designer Elliott Kember pointed out the security flaw through a blog post. Interestingly, a Chrome developer told Kember on a discussion thread on Hacker News that the security flaw is in fact a feature of the browser. He said that the main password boundary for the user was the OS user account and there were vulnerabilities that could be exploited if that is breached.
We'd recommend not to sign-in to Chrome while using a shared computer, but the best option would be to not save passwords through the browser's default passwords manager. Tools like 1Password and LastPass are better ways of storing passwords, and they need a master password before giving you access to your passwords, offering increased security.
Update - Editor's Note: As our readers have pointed out via the comments, Firefox also lets anyone with access to the PC view the passwords by default. However, the reason Firefox was not mentioned - but perhaps should have been as a comparison - is that it lets you set a master password to prevent this from happening.
Further, yes, this is not a new discovery about Chrome and has been around since its initial days - as mentioned in the story. It's great that so many of our readers are aware of this behaviour, but it's still worth highlighting for the large percentage who aren't.
Google's popular Web browser allows you to save your passwords and manage them through a menu in the browser's Settings page. When you click on 'Manage saved passwords' you get a list of your Saved passwords as well as a list of websites where you have instructed the browser to 'never save'. Interestingly, when you click on one of your saved passwords, Google gives you the option to see the password in plain text by clicking on the 'Show' button which is placed along with the listing. It doesn't ask for a confirmation or any additional verification by, say, prompting for your Google account's password.
Once signed in to your Google account on Chrome, the browser pulls all your bookmarks, browsing history and passwords. This means that if you forget to sign out while using Chrome on a shared computer, anyone will be able to access your saved passwords easily. Or someone sitting next to you while you are using the computer can distracting you momentarily. Someone accessing your computer remotely can also see these passwords, if you're not constantly supervising. The intruder can change the password and block access to your service accounts, as well.
Software designer Elliott Kember pointed out the security flaw through a blog post. Interestingly, a Chrome developer told Kember on a discussion thread on Hacker News that the security flaw is in fact a feature of the browser. He said that the main password boundary for the user was the OS user account and there were vulnerabilities that could be exploited if that is breached.
"The only strong permission boundary for your password storage is the OS user account. So, Chrome uses whatever encrypted storage the system provides to keep your passwords safe for a locked account. Beyond that, however, we've found that boundaries within the OS user account just aren't reliable, and are mostly just theater.
Consider the case of someone malicious getting access to your account. Said bad guy can dump all your session cookies, grab your history, install malicious extension to intercept all your browsing activity, or install OS user account level monitoring software. My point is that once the bad guy got access to your account the game was lost, because there are just too many vectors for him to get what he wants.
We've also been repeatedly asked why we don't just support a master password or something similar, even if we don't believe it works. We've debated it over and over again, but the conclusion we always come to is that we don't want to provide users with a false sense of security, and encourage risky behavior. We want to be very clear that when you grant someone access to your OS user account, that they can get at everything. Because in effect, that's really what they get."
We'd recommend not to sign-in to Chrome while using a shared computer, but the best option would be to not save passwords through the browser's default passwords manager. Tools like 1Password and LastPass are better ways of storing passwords, and they need a master password before giving you access to your passwords, offering increased security.
Update - Editor's Note: As our readers have pointed out via the comments, Firefox also lets anyone with access to the PC view the passwords by default. However, the reason Firefox was not mentioned - but perhaps should have been as a comparison - is that it lets you set a master password to prevent this from happening.
Further, yes, this is not a new discovery about Chrome and has been around since its initial days - as mentioned in the story. It's great that so many of our readers are aware of this behaviour, but it's still worth highlighting for the large percentage who aren't.
Comments
For the latest tech news and reviews, follow Gadgets 360 on X, Facebook, WhatsApp, Threads and Google News. For the latest videos on gadgets and tech, subscribe to our YouTube channel. If you want to know everything about top influencers, follow our in-house Who'sThat360 on Instagram and YouTube.
Related Stories
Popular on Gadgets
- Galaxy S24 Series
- MWC 2024
- Apple Vision Pro
- Oneplus 12
- iPhone 14
- Apple iPhone 15
- OnePlus Nord CE 3 Lite 5G
- iPhone 13
- Xiaomi 14 Pro
- Oppo Find N3
- Tecno Spark Go (2023)
- Realme V30
- Best Phones Under 25000
- Samsung Galaxy S24 Series
- Cryptocurrency
- iQoo 12
- Samsung Galaxy S24 Ultra
- Giottus
- Samsung Galaxy Z Flip 5
- Apple 'Scary Fast'
- Housefull 5
- GoPro Hero 12 Black Review
- Invincible Season 2
- JioGlass
- HD Ready TV
- Laptop Under 50000
- Smartwatch Under 10000
- Latest Mobile Phones
- Compare Phones
Latest Gadgets
- Samsung Galaxy C55
- Blackview Hero 10
- Oppo K12
- Vivo Y200i
- Huawei Pura 70 Pro
- Huawei Pura 70
- Vivo V30e
- Itel Super Guru 4G
- Lenovo IdeaPad Pro 5i
- Asus ZenBook Duo 2024 (UX8406)
- Realme Pad 2 Wi-Fi
- Redmi Pad Pro
- boAt Storm Call 3
- Lava ProWatch Zn
- Samsung Samsung Neo QLED 8K Smart TV QN800D
- Samsung Neo QLED 4K Smart TV (QN90D)
- Sony PlayStation 5 Slim Digital Edition
- Sony PlayStation 5 Slim
- Voltas 1.5 Ton 3 Star Split AC (183 Vectra Elegant 4503545)
- Hitachi 1.5 Ton 5 Star Inverter Split AC (RAS.G518PCBISF)
© Copyright Red Pixels Ventures Limited 2024. All rights reserved.

















