- Home
- Internet
- Internet Features
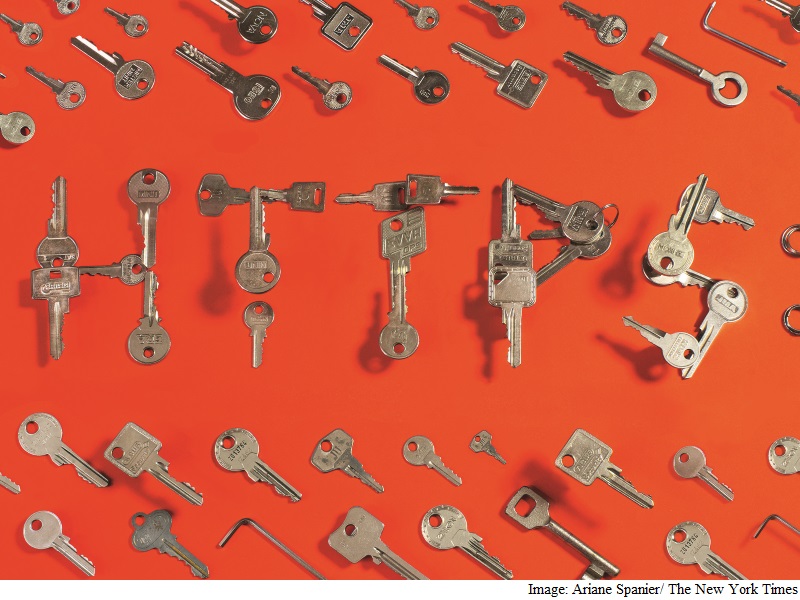
- Encryption, Always Important, Is Now Easy
Encryption, Always Important, Is Now Easy
Whether you visit Amazon's product pages, stream a movie from Netflix or read the tax rules on the Internal Revenue Service's website, marketers and hackers can snoop on everything you do.
But now, the computer industry and the U.S. government have embarked on a major, multifront campaign to have basic Web encryption - known as HTTPS or TLS encryption - more widely adopted.
A nonprofit group backed by several leading technology companies and advocacy groups, including Mozilla, Cisco Systems and the Electronic Frontier Foundation, is offering a free set of services called Let's Encrypt to help website administrators incorporate HTTPS security into their sites.
Tech giants like Google and Apple are also flexing their power to encourage websites and mobile app makers to adopt basic encryption or be penalized in Web searches and the Apple App Store.
And the Obama administration - embarrassed by Edward Snowden's revelations of mass surveillance by the National Security Agency and the theft of federal personnel records by foreign hackers - has ordered all publicly accessible websites run by the executive branch to use HTTPS encryption by the end of 2016.
HTTPS encryption essentially creates a private connection between a user's browser and the website being visited so that the information being exchanged cannot be viewed or modified by an outsider. Typically signified by a lock symbol in the address bar, it is routine on sites intended for the exchange of confidential financial data, such as bank or store checkout pages. Big sites like those owned by Facebook, Yahoo and Google have also adopted such basic encryption in recent years.
(Also see: Apple, Google, and Others Appeal to Obama to Keep Hands Off Encryption)
But millions of websites are unprotected, especially older sites and those whose pages pull in content from third parties, such as news sites that show advertising coming from many sources.
Without encryption, digital trackers can - and do - scoop up detailed information about people's browsing habits on those sites. Some of the snooping is done by marketers looking to build profiles of Web users and some by Internet service providers that want to insert extra ads on Web pages visited by their users.
An unencrypted connection also opens the possibility of a hacker's impersonation of a trusted website for more nefarious reasons, such as to steal personal information.
"When the page you visit is not secure anywhere along the network path, anyone, whether it's the NSA or another government or the ISP, can sniff on your traffic and see what you're browsing," said Jacob Hoffman-Andrews, a senior staff technologist at the Electronic Frontier Foundation, an Internet policy group involved in several projects to promote encryption.
Configuring a new site for HTTPS encryption can be complicated and costly, especially for a small company without a dedicated tech services team.
Let's Encrypt, the new offering from the Internet Security Research Group, is intended to take some of the inconvenience out of the process by offering a complete package of free security services that a website operator can install on the server to easily set up or convert a site to include encryption.
"We want every site on the Web to be able to provide HTTPS," said Hoffman-Andrews, who has been working on the project. "We think that's a value."
The centerpiece of Let's Encrypt is the site certificate, a sort of digital ID card that tells a Web browser like Firefox or Safari that, say, the Chase.com you are visiting after typing the address into your address bar is really the bank and not an impostor. These certificates are sold by hundreds of providers around the world, some more reputable than others, but going through the process of getting a certificate and properly integrating it into your website can be more trouble than many sites want to go through.
The Let's Encrypt team decided to simplify the setup, including getting approval to issue its own certificates. The project began offering its first certificates in September and plans wide-scale issuance in November.
Josh Aas, executive director of the Internet Security Research Group and an engineer on leave from the Mozilla Corp., said that one goal was to remove the excuse that encryption is too hard to put in place.
In the early days of HTTPS encryption, the technology and certificates were expensive to set up and slowed down page loading times significantly. Most websites, especially those that did not handle particularly sensitive information such as financial data, chose not to incorporate it.
But now the installation process is simpler and the consequences of ignoring encryption are greater.
So it's not enough to just encrypt traditionally sensitive pages like online shopping carts. "We need to treat all users' data as if they really care about it," Aas said.
Google, whose search engine serves as the guide to the Internet for so many people, is trying to encourage change through its powerful positions in Web search and online advertising.
Starting last year, Google began raising the ranking of encrypted pages in Web search results and lowering the ranking of unencrypted pages - a subtle nudge to website owners to adopt HTTPS.
The company has also changed its advertising systems to encourage advertisers to serve their ads on encrypted channels.
While a Web user can check for the lock icon to see if a site is secure, apps have no such obvious signaling system. Apple is supporting more security across the board. In the latest version of its operating system for iPhones and iPads, Apple is pushing application developers to use HTTPS to protect communications between apps and the Web.
Apple is not yet penalizing apps that fail to use encryption, but developers expect the company to do so eventually.
The federal government is also waking up to the importance of encryption.
The White House's order in June that all websites run by the executive branch adopt HTTPS encryption covers about 1,300 Web domains, including those of the Centers for Disease Control and Prevention and the National Weather Service.
"The federal government should require strong security for all of its properties," said Eric Mill, a technologist at 18F, the federal team that helped draft the policy.
© 2015 New York Times News Service
For the latest tech news and reviews, follow Gadgets 360 on X, Facebook, WhatsApp, Threads and Google News. For the latest videos on gadgets and tech, subscribe to our YouTube channel. If you want to know everything about top influencers, follow our in-house Who'sThat360 on Instagram and YouTube.
Related Stories
- AI
- iPhone 16 Leaks
- Apple Vision Pro
- Oneplus 12
- iPhone 14
- Apple iPhone 15
- OnePlus Nord CE 3 Lite 5G
- iPhone 13
- Xiaomi 14 Pro
- Oppo Find N3
- Tecno Spark Go (2023)
- Realme V30
- Best Phones Under 25000
- Samsung Galaxy S24 Series
- Cryptocurrency
- iQoo 12
- Samsung Galaxy S24 Ultra
- Giottus
- Samsung Galaxy Z Flip 5
- Apple 'Scary Fast'
- Housefull 5
- GoPro Hero 12 Black Review
- Invincible Season 2
- JioGlass
- HD Ready TV
- Laptop Under 50000
- Smartwatch Under 10000
- Latest Mobile Phones
- Compare Phones
- Vivo Y18e
- Vivo Y18
- Vivo Y38 5G
- Nokia 235 4G (2024)
- Nokia 225 4G (2024)
- Nokia 215 4G (2024)
- Redmi Note 13 Pro+ 5G World Champions Edition
- Infinix GT 20 Pro
- Dell Alienware X16 R2
- Lenovo IdeaPad Pro 5i
- Lenovo Tab K11
- Realme Pad 2 Wi-Fi
- boAt Storm Call 3
- Lava ProWatch Zn
- Samsung Samsung Neo QLED 8K Smart TV QN800D
- Samsung Neo QLED 4K Smart TV (QN90D)
- Sony PlayStation 5 Slim Digital Edition
- Sony PlayStation 5 Slim
- Lloyd 1 Ton 3 Star Inverter Split AC (GLS12I3FWAEV)
- Voltas 1.5 Ton 5 Star Inverter Split AC (185V Vectra Elite)
















