WhatsApp Web Security Flaw Can Affect Up to 200 Million Users: Report
A newly found vulnerability in WhatsApp Web, the Web-based interface of the popular instant messaging client, allows attackers to trick users into executing arbitrary code on their computers, a security firm reports. The vulnerability affects more than 200 million people who use WhatsApp Web. WhatsApp has since updated its Web client to patch the bug in the latest version.
The 'MaliciousCard' vulnerability can be exploited by simply sending a vCard contact card containing malicious code to a victim's account, reports security firm Check Point. Once the victim opens the alleged contact, it starts to distribute bots, ransomware, and other malware files.
Since the business contact card looks perfectly legitimate, it is impossible for a user to know if the contact is riddled with malicious code.
The security firm noted that it informed WhatsApp about the vulnerability, and the messaging service issued an update on August 21 that fixes the bug. WhatsApp Web v0.1.4481 or later are not affected with the vulnerability.
The vulnerability lies in the improper filtering of contact cards sent in the vCard format in older versions of WhatsApp. The attacker can inject a command in the name attribute of the vCard file, separated by the ampersand character. Windows would automatically try to run all lines in the code. It is not known whether Mac users are affected by the vulnerability.
WhatsApp fails to validate the vCard format and the contents of the file, the firm further noted. One could send an executable file and WhatsApp wouldn't be able to flag or block it.
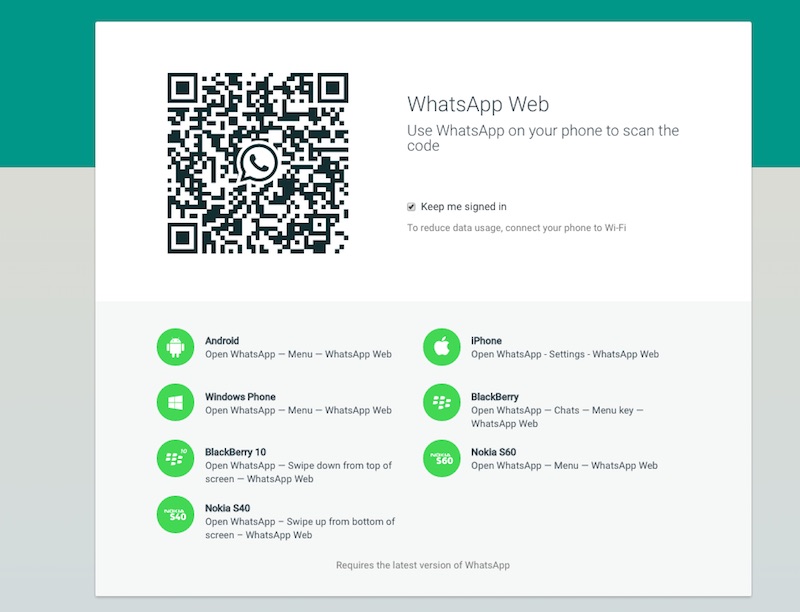
WhatsApp, which is available across multiple platforms, recently announced that it reached 900 million monthly active users. WhatsApp Web, which offers several of the mobile app's functionalities including the ability to send and receive text and audio notes, is used by more than 200 million users.
For the latest tech news and reviews, follow Gadgets 360 on X, Facebook, WhatsApp, Threads and Google News. For the latest videos on gadgets and tech, subscribe to our YouTube channel. If you want to know everything about top influencers, follow our in-house Who'sThat360 on Instagram and YouTube.
Related Stories
- AI
- iPhone 16 Leaks
- Apple Vision Pro
- Oneplus 12
- iPhone 14
- Apple iPhone 15
- OnePlus Nord CE 3 Lite 5G
- iPhone 13
- Xiaomi 14 Pro
- Oppo Find N3
- Tecno Spark Go (2023)
- Realme V30
- Best Phones Under 25000
- Samsung Galaxy S24 Series
- Cryptocurrency
- iQoo 12
- Samsung Galaxy S24 Ultra
- Giottus
- Samsung Galaxy Z Flip 5
- Apple 'Scary Fast'
- Housefull 5
- GoPro Hero 12 Black Review
- Invincible Season 2
- JioGlass
- HD Ready TV
- Laptop Under 50000
- Smartwatch Under 10000
- Latest Mobile Phones
- Compare Phones
- Realme Realme GT Neo 6
- Nokia 3210 4G
- Vivo Y18e
- Vivo Y18
- Vivo Y38 5G
- Nokia 235 4G (2024)
- Nokia 225 4G (2024)
- Nokia 215 4G (2024)
- Dell Alienware X16 R2
- Lenovo IdeaPad Pro 5i
- Apple iPad Pro 13-inch (2024) Wi-Fi
- Apple iPad Pro 13-inch (2024) Wi-Fi + Cellular
- boAt Storm Call 3
- Lava ProWatch Zn
- Samsung Samsung Neo QLED 8K Smart TV QN800D
- Samsung Neo QLED 4K Smart TV (QN90D)
- Sony PlayStation 5 Slim Digital Edition
- Sony PlayStation 5 Slim
- LG 1.5 Ton 3 Star Inverter Window AC (TW-Q18WUXA)
- Godrej 1.1 Ton 3 Star Inverter Split AC (SIC 13DTC3 WWB)
















