'Popular Android Browsers Dolphin and Mercury Are Vulnerable'
Major security vulnerabilities have been found in Dolphin and Mercury Android browsers. Security enthusiast Rotologix has revealed zero-day flaws in the Web browsers, which if exploited, allows attackers to perform remote code execution.
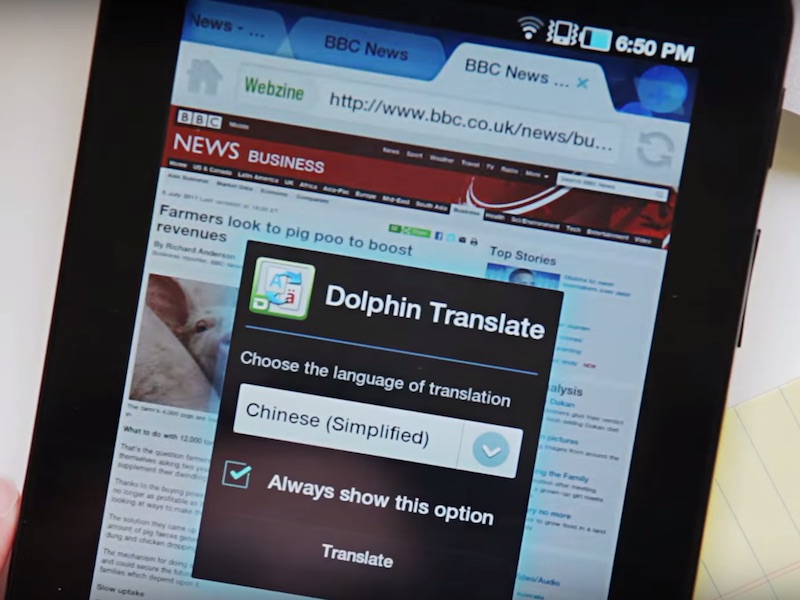
The Dolphin and Mercury browsers are quite popular on Android, racking in over 100 million users. Specifically, the Dolphin remote code execution exploit allows an attacker to replace the browser's theme package with an infected counterpart.
Going further in, the exploit allows an attacker to modify the network traffic, which allows the person to modify the functionality of downloading and applying new themes to the browser. Once affected, a victim is only required to select, download, and apply a new Dolphin browser theme. The Dolphin browser hasn't been updated since July, suggesting that all users are likely affected by the zero-day vulnerability.
"An attacker with the ability to control the network traffic for users of the Dolphin browser for Android, can modify the functionality of downloading and applying new themes for the browser," Rotologix wrote in a blog post. "Through the exploitation of this functionality, an attacker can achieve an arbitrary file write, which can then be turned into code execution within the context of the browser on the user's device," he added.
Moving on, Rotologix says that Mercury browser for Android is affected with an insecure Intent URI scheme implementation and a path traversal vulnerability that provides support to the Wi-Fi Transfer feature. "Chaining these vulnerabilities together can allow a remote attacker to perform arbitrary reading and writing of files within the Mercury Browser's data directory," he added.
For the latest tech news and reviews, follow Gadgets 360 on X, Facebook, WhatsApp, Threads and Google News. For the latest videos on gadgets and tech, subscribe to our YouTube channel. If you want to know everything about top influencers, follow our in-house Who'sThat360 on Instagram and YouTube.
Related Stories
- AI
- iPhone 16 Leaks
- Apple Vision Pro
- Oneplus 12
- iPhone 14
- Apple iPhone 15
- OnePlus Nord CE 3 Lite 5G
- iPhone 13
- Xiaomi 14 Pro
- Oppo Find N3
- Tecno Spark Go (2023)
- Realme V30
- Best Phones Under 25000
- Samsung Galaxy S24 Series
- Cryptocurrency
- iQoo 12
- Samsung Galaxy S24 Ultra
- Giottus
- Samsung Galaxy Z Flip 5
- Apple 'Scary Fast'
- Housefull 5
- GoPro Hero 12 Black Review
- Invincible Season 2
- JioGlass
- HD Ready TV
- Laptop Under 50000
- Smartwatch Under 10000
- Latest Mobile Phones
- Compare Phones
- Vivo Y38 5G
- Nokia 235 4G (2024)
- Nokia 225 4G (2024)
- Nokia 215 4G (2024)
- Redmi Note 13 Pro+ 5G World Champions Edition
- Infinix GT 20 Pro
- Oppo A60
- Realme C65 5G
- Dell Alienware X16 R2
- Lenovo IdeaPad Pro 5i
- Realme Pad 2 Wi-Fi
- Redmi Pad Pro
- boAt Storm Call 3
- Lava ProWatch Zn
- Samsung Samsung Neo QLED 8K Smart TV QN800D
- Samsung Neo QLED 4K Smart TV (QN90D)
- Sony PlayStation 5 Slim Digital Edition
- Sony PlayStation 5 Slim
- Lloyd 1 Ton 3 Star Inverter Split AC (GLS12I3FWAEV)
- Voltas 1.5 Ton 5 Star Inverter Split AC (185V Vectra Elite)















