Nokia's Xpress Browser draws criticism over the way it handles HTTPS data
By Kunal Dua | Updated: 11 January 2013 17:24 IST

Advertisement
Nokia has been pushing its Xpress Browser, found in feature phones and the popular Asha series of phones, at every opportunity. The company claims the browser offers up to 90% savings in data costs by compressing data before transmission. Now, the browser is under criticism after the way it handles HTTPS traffic was brought to light.
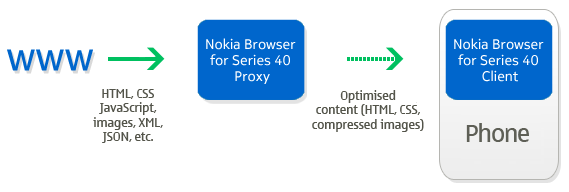
Security blogger Gaurang K Pandya first wrote about the browser in December, highlighting that it was forcing traffic to go via Nokia's proxy server. No surprises there. All browsers which compress data - including Opera Mini and Amazon Silk - employ the same technique. In fact, Nokia's page linked above includes this nifty little image clearly depicting the same.
The outcry started when Pandya highlighted that Xpress Browser was routing secure HTTPS traffic via Nokia servers as well.
When you visit a website using your PC or mobile, the request is sent to the website's server, which responds with the data present on that page. The communication doesn't happen directly between your PC and the website's server, and the request as well as the response are sent via multiple intermediate servers.
Most traffic on the Web is sent over the insecure HTTP protocol (e.g. https://www.gadgets360.com), which means that it can be 'seen' by any one of these intermediaries. The HTTPS protocol (e.g. https://www.google.com) adds a secure layer on top of HTTP that mandates encryption of data exchanged between the two machines, which prevents any intermediaries from snooping in. Another important element of the HTTPS protocol are certificates, which are used to confirm the identity of machines. HTTPS is used for anything that requires secure communication, like transmitting credit card information or bank details.
Nokia's Xpress Browser, and indeed Opera Mini (which talks about the topic in detail in its FAQ) redirect all HTTP and HTTPS communication via their proxy servers. All your HTTPS requests are decrypted by their proxy, and re-encrypted before forwarding them to the secure site. The server's response is then intercepted by the proxy, decrypted and re-encrypted before sending back to the browser. The apps reportedly use pre-installed certificates to 'trick' the browser into trusting the data that is being sent by the proxy instead of the original site.
This means both Nokia and Opera can, at least theoretically, look at, and thus, store, your confidential data. Opera clearly mentions it does not collect any data in its FAQ. The terms of use of Nokia's browser weren't so clear, which sparked an outrage after Pandya shared his findings.
Nokia was forced to issued the following statement, clarifying it does not collect any data.
While that, along with Nokia's statement, should calm the nerves of most users, we believe a bit more time spent in educating users and having "sensible defaults" would go much farther in preventing such controversies from erupting in the future. Browsers like Amazon Silk leave HTTPS communication untouched even when they compress HTTP communication, and we believe that is a sensible way to go.
Security blogger Gaurang K Pandya first wrote about the browser in December, highlighting that it was forcing traffic to go via Nokia's proxy server. No surprises there. All browsers which compress data - including Opera Mini and Amazon Silk - employ the same technique. In fact, Nokia's page linked above includes this nifty little image clearly depicting the same.
The outcry started when Pandya highlighted that Xpress Browser was routing secure HTTPS traffic via Nokia servers as well.
When you visit a website using your PC or mobile, the request is sent to the website's server, which responds with the data present on that page. The communication doesn't happen directly between your PC and the website's server, and the request as well as the response are sent via multiple intermediate servers.
Most traffic on the Web is sent over the insecure HTTP protocol (e.g. https://www.gadgets360.com), which means that it can be 'seen' by any one of these intermediaries. The HTTPS protocol (e.g. https://www.google.com) adds a secure layer on top of HTTP that mandates encryption of data exchanged between the two machines, which prevents any intermediaries from snooping in. Another important element of the HTTPS protocol are certificates, which are used to confirm the identity of machines. HTTPS is used for anything that requires secure communication, like transmitting credit card information or bank details.
Nokia's Xpress Browser, and indeed Opera Mini (which talks about the topic in detail in its FAQ) redirect all HTTP and HTTPS communication via their proxy servers. All your HTTPS requests are decrypted by their proxy, and re-encrypted before forwarding them to the secure site. The server's response is then intercepted by the proxy, decrypted and re-encrypted before sending back to the browser. The apps reportedly use pre-installed certificates to 'trick' the browser into trusting the data that is being sent by the proxy instead of the original site.
This means both Nokia and Opera can, at least theoretically, look at, and thus, store, your confidential data. Opera clearly mentions it does not collect any data in its FAQ. The terms of use of Nokia's browser weren't so clear, which sparked an outrage after Pandya shared his findings.
Nokia was forced to issued the following statement, clarifying it does not collect any data.
We take the privacy and security of our consumers and their data very seriously. The compression that occurs within the Nokia Xpress Browser means that users can get faster web browsing and more value out of their data plans. Importantly, the proxy servers do not store the content of web pages visited by our users or any information they enter into them. When temporary decryption of HTTPS connections is required on our proxy servers, to transform and deliver users' content, it is done in a secure manner.Meanwhile, Pandya claims that Nokia has issued an update to its browser that means it is no longer decrypting the data on its servers, but the traffic is still flowing via its servers.
Nokia has implemented appropriate organizational and technical measures to prevent access to private information. Claims that we would access complete unencrypted information are inaccurate.
We aim to be completely transparent on privacy practices. As part of our policy of continuous improvement we will review the information provided in the mobile client in case this can be improved.
While that, along with Nokia's statement, should calm the nerves of most users, we believe a bit more time spent in educating users and having "sensible defaults" would go much farther in preventing such controversies from erupting in the future. Browsers like Amazon Silk leave HTTPS communication untouched even when they compress HTTP communication, and we believe that is a sensible way to go.
Amazon Silk routes secure (SSL) web page requests directly from your computer to origin servers so they do not pass through Amazon servers.Even if companies like Nokia and Opera want to offer the ability to compress HTTPS data as a genuine benefit to users, they should have it as an application preference that is turned off by default. The users should be told exactly what this option entails before they flip that switch on.
Affiliate links may be automatically generated - see our ethics statement for details.
Comments
For the latest tech news and reviews, follow Gadgets 360 on X, Facebook, WhatsApp, Threads and Google News. For the latest videos on gadgets and tech, subscribe to our YouTube channel. If you want to know everything about top influencers, follow our in-house Who'sThat360 on Instagram and YouTube.
Related Stories
Popular on Gadgets
- Galaxy S24 Series
- MWC 2024
- Apple Vision Pro
- Oneplus 12
- iPhone 14
- Apple iPhone 15
- OnePlus Nord CE 3 Lite 5G
- iPhone 13
- Xiaomi 14 Pro
- Oppo Find N3
- Tecno Spark Go (2023)
- Realme V30
- Best Phones Under 25000
- Samsung Galaxy S24 Series
- Cryptocurrency
- iQoo 12
- Samsung Galaxy S24 Ultra
- Giottus
- Samsung Galaxy Z Flip 5
- Apple 'Scary Fast'
- Housefull 5
- GoPro Hero 12 Black Review
- Invincible Season 2
- JioGlass
- HD Ready TV
- Laptop Under 50000
- Smartwatch Under 10000
- Latest Mobile Phones
- Compare Phones
Latest Gadgets
- Huawei Pura 70 Pro
- Huawei Pura 70
- Vivo V30e
- Itel Super Guru 4G
- Huawei Pura 70 Pro+
- Huawei Pura 70 Ultra
- Tecno Camon 30 Premier 5G
- Motorola Edge 50 Fusion
- Asus ZenBook Duo 2024 (UX8406)
- Dell Inspiron 14 Plus
- Realme Pad 2 Wi-Fi
- Redmi Pad Pro
- Cult Shock X
- Fire-Boltt Oracle
- Samsung Samsung Neo QLED 8K Smart TV QN800D
- Samsung Neo QLED 4K Smart TV (QN90D)
- Sony PlayStation 5 Slim Digital Edition
- Sony PlayStation 5 Slim
- Voltas 1.5 Ton 3 Star Split AC (183 Vectra Elegant 4503545)
- Hitachi 1.5 Ton 5 Star Inverter Split AC (RAS.G518PCBISF)
© Copyright Red Pixels Ventures Limited 2024. All rights reserved.

















